AI Review for Business Associate Agreements (BAAs)
What is a Business Associate Agreement?
Business Associate Agreements (BAAs) are contracts pertaining to the use and disclosure of protected health information (PHI) that are legally mandated by the Health Insurance Portability and Accountability Act of 1996 (HIPAA), as amended, and its implementing regulations. They are to be used by healthcare providers, health plans, and health care clearinghouses ("Covered Entities") when they are disclosing PHI to a "Business Associate," which is an entity or individual, other than a member of the workforce of a Covered Entity, who performs functions or activities on behalf of, or provides certain services to, the Covered Entity that involve access by the Business Associate to PHI. BAAs are also used between a Business Associate and its subcontractors that create, receive, maintain, or transmit PHI on behalf of the Business Associate.
A BAA must include specific information and language that is set forth in the parts of the Code of Federal Regulations that implement HIPAA. Some of these mandated provisions pertain to the permitted uses of PHI by the Business Associate, the protection to be afforded the PHI, access to the PHI, the reporting of unauthorized use or disclosure of the PHI, termination of the agreement, and return or destruction of the PHI. The parties may also choose to include additional clauses such as data ownership, audit rights, and indemnification.
BAAs are applicable to the Healthcare and HealthTech industries.
Why Use a Business Associate Agreement?
There are several key reasons why Covered Entities and Business Associates should use BAAs:
- Legal Compliance: The use of BAAs is legally mandated by HIPAA and its implementing regulations. Failure to have a BAA in place when required can result in significant fines and penalties.
- PHI Protection: BAAs outline the responsibilities of the Business Associate in protecting the privacy and security of PHI. This helps ensure that sensitive patient information is handled appropriately and is not subject to unauthorized use or disclosure.
- Clarification of Roles and Responsibilities: BAAs clearly define the roles and responsibilities of the Covered Entity and the Business Associate with respect to PHI. This helps avoid misunderstandings and ensures that both parties are aware of their obligations.
- Risk Mitigation: By outlining the permitted uses of PHI and the steps that must be taken in the event of an unauthorized use or disclosure, BAAs help mitigate the risk of HIPAA violations and data breaches.
- Establishing Trust: BAAs demonstrate to patients that their healthcare providers are taking the necessary steps to protect their sensitive information. This can help establish trust and improve patient relationships.
What Should Be Included in a Business Associate Agreement?
A BAA must include specific provisions that are mandated by HIPAA and its implementing regulations. These provisions pertain to:
- Permitted uses and disclosures of PHI by the Business Associate
- Safeguards to be implemented to protect PHI
- Reporting of unauthorized uses or disclosures of PHI
- Access to PHI by individuals
- Amendment of PHI
- Accounting of disclosures of PHI
- Termination of the agreement
- Return or destruction of PHI upon termination of the agreement
In addition to these legally required provisions, there are optional provisions that, while not required, are often included in BAAs as best practice. Some key considerations for these optional provisions include:
- Definitions: Though the definitions of most terms of art used in a BAA can be found in the regulations, definitions in BAAs may misdescribe the regulatory definition (modifying the meaning of provisions in which they are included) and thus, BAA definitions sections are thoroughly reviewed and often negotiated.
- Data Use Agreement: Covered Entities and BAAs using or disclosing PHI are legally obligated to use and disclose only the minimum information necessary to achieve the purpose of that use or disclosure. As such, it is important that they use Limited Data Sets (which is a type of PHI that is partially de-identified, as set forth in regulations) if they can achieve their aims with this safer type of PHI. However, disclosure of Limited Data Sets mandates the use of a Data Use Agreement (DUA). While these are often stand-alone agreements, our BAA helpfully includes the required elements of a DUA.
- Data Ownership: Covered Entities will often specify that though they are transferring or disclosing the PHI to the Business Associate, no transfer of ownership of the PHI to the BAA is occurring.
- Audit: The Covered Entity often demands the right to inspect and audit Business Associate's facilities, systems, books, and records; or that the Business Associate provide it with a copy of its most recent independent HIPAA compliance report (AT-C 315), HITRUST certification, or other mutually agreed upon independent, standards-based third-party audit report.
- Cybersecurity Measures: While the federal regulations mandate that both parties implement and document administrative, physical, and technical safeguards in order to protect PHI, a Covered Entity may choose to specifically state in the BAA the types of cybersecurity measures that it will require of the Business Associate, a standard which may be greater than the minimum standards set forth in the regulations.
Checklist for a Good Business Associate Agreement
To ensure that your BAA is effective, comprehensive, and legally compliant, use this checklist:
- Include all legally mandated provisions
- Clearly define terms and definitions
- Include a Data Use Agreement if applicable
- Specify data ownership
- Include audit rights for the Covered Entity
- Specify required cybersecurity measures
- Tailor the agreement to the specific relationship and services involved
- Have the agreement reviewed by legal counsel specializing in healthcare law
- Ensure the agreement is signed by authorized representatives of both parties
- Regularly review and update the agreement as needed
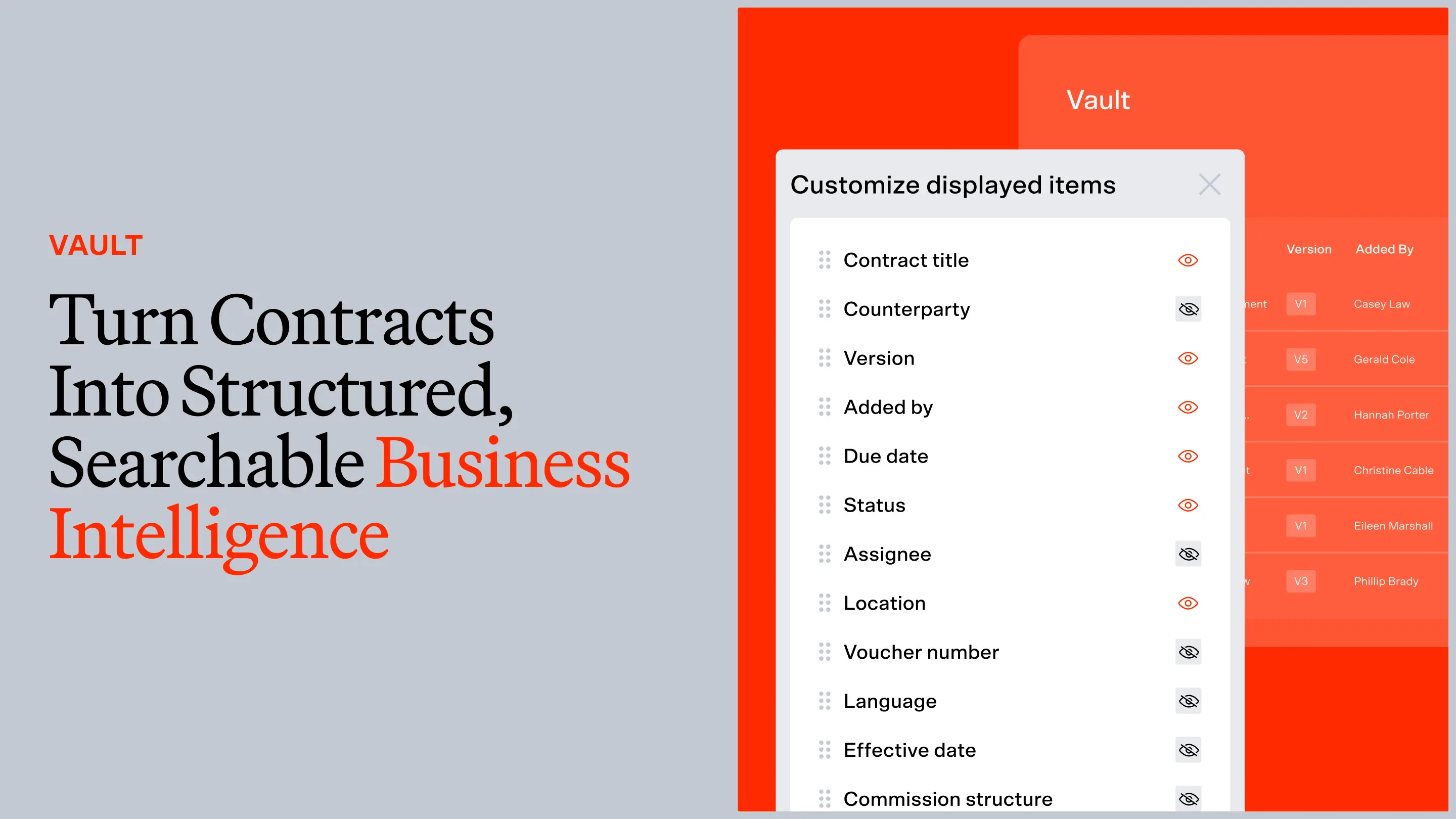
AI Contract Review for Business Associate Agreements
To give you a sense for the benefits of leveraging legal contract analysis software trained by lawyers, we’ve selected some sample language our software presents to customers during a review. Keep in mind that these are static in this overview, but dynamic in our software - meaning our AI identifies the key issues and proactively surfaces alerts based on importance level and position (company, 3rd party, or neutral) and provides suggested revisions that mimic the style of the contract and align with party names and defined terms.
These samples represent a small sample of the pre-built, pre-trained Legal AI Contract Review solution for Business Associate Agreements. If you’d like to see more, we invite you to book a demo.
PERMITTED USES AND DISCLOSURES
For: Business Associate
Alert: May be missing an article covering the permitted uses and disclosures of PHI by the business associate.
Guidance: To maintain compliance with HIPAA and safeguard the privacy and security of PHI, it is essential to include specific language in a BAA that delineates the permitted uses and disclosures of PHI by the Business Associate. This inclusion ensures that both parties understand their respective responsibilities and limitations concerning the handling of PHI and that the BAA contains the required elements under Title 45 of the Code of Federal Regulations Section 164.504(e).
Specifying the reasons the Business Associate can use or disclose the PHI that the Covered Entity anticipates providing under the BAA ensures that the Business Associate will be cognizant of its obligations. This, in turn, reduces the risk of unauthorized uses or disclosures of the PHI, which could have dire consequences for the privacy of the individuals about which the PHI pertains and potentially damage the Business Associate's reputation and relationship with the Covered Entity.
Sample Language:
USES AND DISCLOSURES OF PHI BY BUSINESS ASSOCIATE
1. Permitted Uses and Disclosures. Except as otherwise provided in this Agreement, BUSINESS ASSOCIATE may use or disclose PHI only to perform functions, activities, or services specified in this Agreement or as necessary to perform BUSINESS ASSOCIATE’s obligations under the Contract for, or on behalf of, COVERED ENTITY, provided that such use or disclosure would not violate HIPAA if done by COVERED ENTITY.
2. Specific Use and Disclosure Provisions. Additionally, BUSINESS ASSOCIATE may:
2.1 use and disclose PHI for the proper management and administration of the BUSINESS ASSOCIATE or to carry out the legal responsibilities of the BUSINESS ASSOCIATE, provided that disclosures are required by law, or the BUSINESS ASSOCIATE obtains reasonable assurances from the person to whom the information is disclosed that it will remain confidential and will be used or further disclosed only as required by law or for the purpose for which it was disclosed to the person.
2.2 use or disclose PHI to provide Data Aggregation services to COVERED ENTITY, if such services are to be provided by BUSINESS ASSOCIATE for the healthcare operations of COVERED ENTITY pursuant to the Contract between the Parties.
2.3 De-identify any and all PHI received by BUSINESS ASSOCIATE under this Agreement, provided that the de-identification conforms to the requirements of HIPAA.
2.4 disclose PHI to report violations of law to appropriate federal and state authorities, consistent with 45 C.F.R. 164.502 (j)(1).
ELECTRONIC TRANSMISSION STANDARDS
For: Covered Entity
Alert: May be missing an article requiring the business associate to comply with all applicable electronic transactions and code sets standards under HIPAA.
Guidance: HIPAA requires covered entities to conduct standard transactions with one another. Conducting a transaction as a “standard transaction” includes compliance with the set data standard and affiliated operating rules, code sets, and unique identifiers for the particular transaction. For example, if a covered entity uses a business associate to conduct any portion of a transaction for which a standard has been adopted, the covered entity must require their business associate (and its agents and subcontractors) to comply with that standard, pursuant to 45 CFR § 162.923(c). Simply put, the inclusion of a business associate in a transaction does not relieve a covered entity of its responsibility to comply with HIPAA because a business associate is acting on behalf of a covered entity.
Additionally, adherence to HIPAA electronic transactions and code standards is vital for maintaining patient privacy, preventing data breaches, and preserving the integrity of business operations. For example, when a Business Associate processes electronic claims on behalf of a company, compliance with these standards ensures secure and accurate transmission of PHI, reducing the risk of data breaches and potential legal liabilities.
In addition to HIPAA, businesses should consider the Privacy Rule, Security Rule, and the Standards for Electronic Transactions, which provide a legal framework for protecting PHI and maintaining data security. HHS has adopted standards for Health Care Claims or Equivalent Encounter Information (45 CFR § 162.1101-1102), Eligibility for a Health Plan (45 CFR § 162.1201-1203), Referral Certification and Authorization (45 CFR § 162.1301-1302), Health Care Claim Status (45 CFR §162.1401-1403), Enrollment or Disenrollment in a Health Plan (45 CFR § 162.1501-1502), Health Care Electronic Funds Transfer and Remittance Advice (45 CFR § 162.1601-1603), Health Plan Premium Payments, Coordination of Benefits (45 CFR § 162.1701-1702), and Medicaid Pharmacy Subrogation Transactions (45 CFR § 162.1901-1902).
Specific parameters for covered entities also exist.
Sample Language:
ELECTRONIC TRANSMISSION STANDARDS
BUSINESS ASSOCIATE, along with its Workforce and Subcontractors, shall comply with all applicable electronic transactions and code sets standards under HIPAA.
CYBERSECURITY MEASURES
For: Covered Entity
Alert: May be missing an article regarding the business associate's obligation to maintain cybersecurity measures.
Guidance: In the context of a BAA, it is essential to obligate the Business Associate to implement and maintain appropriate cybersecurity measures to protect the confidentiality, integrity, and availability of PHI shared between the parties. This obligation is crucial as it helps minimize the risk of data breaches and potential legal liabilities for the parties involved.
For instance, if a Business Associate providing EHR services experiences a cyberattack, the BAA should include language obligating the Business Associate to maintain certain cybersecurity measures. This would hold the Business Associate accountable for any failure to implement and maintain those measures, potentially shielding the parties from liability and financial losses.
Relevant statutes or laws to consider in this context include HIPAA and the HITECH Act, which establish standards for the protection of PHI and impose penalties for non-compliance. Incorporating the proposed suggestion into the BAA can help ensure compliance with these regulations and reduce the risk of penalties and legal liabilities.
Additionally, HIPAA's Breach Notification Rule is a significant regulation that applies to the primary legal principle. This rule requires covered entities and Business Associates to provide notification following a breach of unsecured PHI. By incorporating language obligating the Business Associate to maintain certain cybersecurity measures in a BAA, the likely compliance with HIPAA Security Rule is improved, the risk of breaches is reduced, and the likelihood of triggering the requirements under the Breach Notification Rule is in turn lowered.
Sample Language:
CYBERSECURITY MEASURES
1. Necessary Steps. BUSINESS ASSOCIATE agrees to take reasonably necessary steps to ensure the continuous security of all computerized data systems containing COVERED ENTITY’s PHI, and to provide data security procedures for the use of COVERED ENTITY at the end of the Term. These steps shall include, at a minimum:
1.1 Compliance with HIPAA. Achieving and maintaining compliance with the Security Rule (45 C.F.R. Parts 160 and 164) in conducting operations on behalf of COVERED ENTITY under this Agreement. Furthermore, to the extent feasible, BUSINESS ASSOCIATE will ensure that the technology safeguards used by BUSINESS ASSOCIATE to secure PHI will render such PHI unusable, unreadable, and indecipherable to individuals unauthorized to acquire or otherwise have access to such PHI in accordance with the guidance promulgated by the HHS, including the standards adopted by HHS from the National Institute for Standards and Technology concerning the protection of identifiable data such as PHI.
1.2 Compliance with Security Standards of COVERED ENTITY. If BUSINESS ASSOCIATE stores COVERED ENTITY’s PHI, BUSINESS ASSOCIATE will comply with the safeguard provisions mandated by COVERED ENTITY. If the above safeguard standards change, and after BUSINESS ASSOCIATE receives notice of any changes, BUSINESS ASSOCIATE agrees to work in good faith to determine if BUSINESS ASSOCIATE can comply with the changes, and if BUSINESS ASSOCIATE determines that it cannot comply with the changes, COVERED ENTITY and BUSINESS ASSOCIATE agree that this Agreement and the Contract may be immediately terminated by either Party.
1.3 Background Check. Before a member of BUSINESS ASSOCIATE’s Workforce may access COVERED ENTITY’s PHI and depending on the nature of the scope of work, a thorough background check of that Workforce member may be conducted, with evaluation of the results to assure that there is no indication that the Workforce member may present a risk to the security or integrity of confidential data or a risk for theft or misuse of confidential data. BUSINESS ASSOCIATE shall retain each Workforce member's background check documentation for a period of [●●] ([●●]) years following Contract termination.
1.4 Designated ISO. BUSINESS ASSOCIATE shall designate an Information Security Officer to oversee its data security program who shall be responsible for carrying out the requirements of this section, including performance and documentation of risk assessments, and for communicating on security matters with COVERED ENTITY.
2. Liability for Requirements. BUSINESS ASSOCIATE acknowledges that (a) the foregoing safeguards, policies, and standards shall apply to BUSINESS ASSOCIATE in the same manner that such requirements apply to COVERED ENTITY, and (b) BUSINESS ASSOCIATE may be held liable under the civil and criminal enforcement provisions set forth at 42 U.S.C. 1320d-5 and 1320d-6, as amended from time to time, for failing to comply with HIPAA.
Best Practices for Using Business Associate Agreements
To make the most of your BAAs and ensure their effectiveness, follow these best practices:
- Identify All Business Associates: Conduct a thorough assessment to identify all vendors and service providers that qualify as Business Associates under HIPAA. This includes any entity that creates, receives, maintains, or transmits PHI on your behalf.
- Establish a BAA Process: Develop a standardized process for executing BAAs. This should include procedures for reviewing and negotiating the agreements, obtaining signatures, and securely storing the executed agreements.
- Train Your Staff: Ensure that all relevant staff members are trained on HIPAA requirements and the importance of BAAs. They should understand when a BAA is required and what their responsibilities are under these agreements.
- Monitor Compliance: Regularly monitor your Business Associates' compliance with the terms of the BAA. This may involve conducting audits, reviewing compliance reports, or requiring self-assessments.
- Update as Needed: HIPAA regulations and guidance can change over time. Regularly review your BAAs and update them as needed to ensure ongoing compliance.
- Respond Promptly to Incidents: In the event of a data breach or other incident involving a Business Associate, respond promptly and in accordance with the terms of the BAA. This may include conducting an investigation, providing notifications, and taking corrective action.
Conclusion
Business Associate Agreements are a critical component of HIPAA compliance. They ensure that PHI is appropriately protected when it is being handled by a Business Associate on behalf of a Covered Entity. By clearly defining the responsibilities and obligations of each party, BAAs help mitigate the risk of unauthorized use or disclosure of PHI.
To ensure the effectiveness of your BAAs, it's important to include all legally required provisions, as well as key optional provisions such as definitions, data use agreements, data ownership, audit rights, and cybersecurity requirements. The agreement should be tailored to your specific circumstances, reviewed by legal counsel, and regularly updated as needed.
By following best practices for executing and managing BAAs, healthcare organizations can build strong, compliant relationships with their Business Associates and better protect the privacy and security of their patients' sensitive information.
Experience LegalOn Today


.svg)



.webp)